Difference Between Disassembly and Decompilation
Explore the difference between disassembly and decompilation, definitions, outputs, use cases, and practical guidance for reverse engineering, firmware analysis, and software debugging.
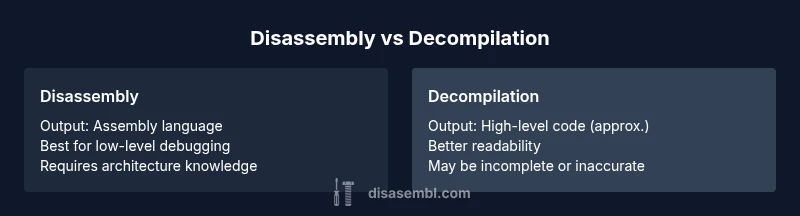
Disassembly translates binary or machine code into assembly language, offering a precise, low-level view of a program’s instructions. Decompilation, by contrast, attempts to reconstruct high-level source code from compiled binaries, producing a readable but approximate representation. Understanding this distinction is essential for effective reverse engineering, firmware analysis, and debugging, as the outputs differ in readability, fidelity, and legal considerations. According to Disasembl, choosing the right approach hinges on the required level of detail, the legality of the task, and the target system architecture.
Defining the Landscape: Disassembly vs Decompilation
Disassembly and decompilation are two cornerstone techniques in reverse engineering, but they operate at different levels of abstraction. Disassembly converts a binary into assembly language—human-readable, instruction-level representations that map one-to-one with machine code. Decompilation aims higher, attempting to recreate source-level constructs like variables, functions, and control flow from the same binary. The Disasembl team emphasizes that the core distinction is not about legality or speed alone; it is about the fidelity of representation and the level of insight you gain. For practitioners, this means knowing when to inspect raw instructions versus when to read a reconstructed, but imperfect, high-level narrative of the program’s intent. In practical terms, disassembly is indispensable for precise debugging and hardware-tied analysis, while decompilation is favored when you need a more approachable understanding of logic and behavior. Through this lens, the difference between disassembly and decompilation becomes a matter of depth and audience—assembly for engineers, higher-level approximations for analysts and learners.
This distinction matters across fields—firmware research, security auditing, competitive analysis, and educational settings. Disasembl’s guidance highlights how the decision influences workflow, tool selection, and the amount of manual reconstruction required to interpret results. In short, disassembly and decompilation are complementary tools in the reverse-engineering toolkit, each serving distinct goals and producing outputs that shape subsequent analysis.
bold
Comparison
| Feature | Disassembly | Decompilation |
|---|---|---|
| Output form | Assembly language (low-level, instruction-accurate) | High-level code (approximate, readable) |
| Typical use cases | Low-level debugging, firmware review, hardware-aware analysis | Understanding binary intent, recovering high-level structure |
| Accuracy of results | Deterministic at instruction level; mapping is explicit | Often imperfect; patterns guessed; structure reconstructed rather than exact |
| Readability and maintainability | Difficult to read; requires assembly knowledge | More readable; easier to discuss at a conceptual level |
| Tooling complexity | Requires instruction set knowledge, symbol info (where available) | Relies on heuristics, pattern recognition, and control-flow recovery |
| Reversibility and traceability | Direct trace to machine code and instructions | Traceable to pseudo-source constructs but not exact original code |
| Legal/ethical considerations | Legality depends on jurisdiction and context; generally accepted for analysis | Legal constraints often restrict recovery of original source; use caution |
Benefits
- Provides precise, instruction-level insight for debugging and hardware interfaces
- Offers quicker comprehension of intent through higher-level abstractions
- Supports rigorous static analysis and vulnerability assessment
- Helps non-experts grasp program behavior with readable outputs
Drawbacks
- Decompilation outputs can be incomplete or inaccurate, leading to misinterpretation
- Disassembly requires strong knowledge of assembly language and architecture
- Both techniques can raise licensing, IP, and ethical concerns depending on jurisdiction
- Tools may produce noisy results that require substantial manual refinement
Disassembly offers precision for low-level analysis; decompilation provides readability for higher-level understanding.
If you need exact behavior and hardware-level insight, disassembly is the safer choice. If your goal is to quickly grasp overall logic without wrestling with instruction details, decompilation is advantageous—though expect approximations and potential gaps.
Got Questions?
What is the main difference between disassembly and decompilation?
Disassembly converts binaries into assembly language, yielding a precise, low-level representation. Decompilation attempts to reconstruct high-level source code from the same binaries, which is more readable but may be inaccurate or incomplete. Both serve reverse-engineering goals but at different levels of abstraction.
Disassembly gives you exact machine-level instructions in assembly, while decompilation tries to rewrite those instructions as readable code, though not perfectly.
When should I use disassembly instead of decompilation?
Use disassembly when accuracy and hardware-specific behavior matter, such as firmware analysis, vulnerability assessment, or debugging at the instruction level. It is essential when you must understand exact control flow, registers, and instruction effects.
Use disassembly when you need exact instructions and hardware behavior; it’s the go-to for low-level debugging.
Are decompiled outputs reliable?
Decompiled outputs are approximations. They can reveal intent and structure, but variable names, control flow, and language constructs are often reconstructed and may not match the original source exactly. Expect omissions and inaccuracies.
Decompiled code is helpful for understanding, but it’s not guaranteed to be exact.
What legal issues surround reverse engineering?
Reverse engineering laws vary by jurisdiction. In many places, it’s permitted for interoperability or security research, but there are restrictions related to copyright, licensing, and circumvention of protections. Always verify applicable laws before proceeding.
Check local laws; reverse engineering can be restricted by copyright or licensing in some regions.
What kinds of tools are used for these tasks?
Disassembly uses disassemblers and instruction decoders; decompilation relies on decompilers that attempt to reconstruct source-like structures. Both rely on static analysis techniques and, sometimes, dynamic analysis to validate results.
Tools separate by level: disassemblers for machine code and decompilers for higher-level representations.
What to Remember
- Disassembly targets machine-level code (assembly) for precise debugging
- Decompilation aims to recreate high-level code from binaries
- Choose disassembly for accuracy; choose decompilation for readability
- Be mindful of legal and ethical boundaries when reverse engineering
- Expect some manual analysis to bridge gaps in decompiled outputs