Difference Between Build and Release: A Practical Comparison
An analytical, objective comparison of build vs release in software delivery, detailing definitions, workflows, risks, and best practices to help teams optimize their delivery pipelines.
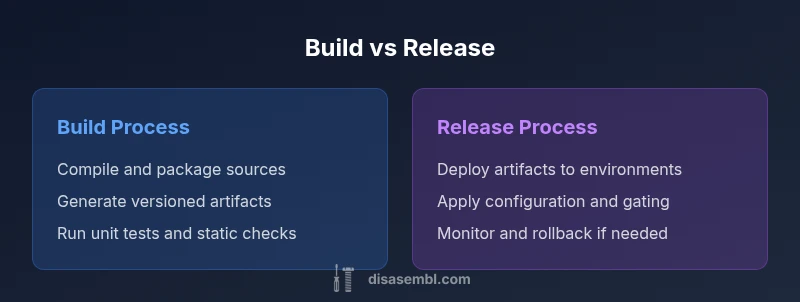
The difference build and release lies in scope and purpose: build focuses on turning code changes into executable artifacts, while release focuses on delivering those artifacts safely into production or other environments. A well-structured approach separates these phases but coordinates them via automated pipelines, governance, and traceable artifacts. In practice, teams blend build and release through CI/CD to optimize feedback loops, minimize risk, and accelerate delivery. The goal is to create repeatable, auditable processes that scale with project complexity.
Defining Build and Release: Core Concepts
In modern software engineering, it helps to distinguish between a build and a release, even though the terms are often used interchangeably in casual discussion. The build is the process of turning source code into a set of executable artifacts—binaries, containers, or package files—that are self-contained and ready for deployment. A build typically includes compilation, linking, packaging, and metadata generation, along with automated checks such as unit tests and static analysis. By contrast, a release is the act of moving those artifacts into a target environment—development, staging, or production—often accompanied by configuration, approvals, and monitoring. The intent of a release is to make value visible to users, not just to generate artifacts. Understanding the difference build and release helps teams assign ownership, design appropriate controls, and measure success at the right stage of the lifecycle. According to Disasembl, clarity in these definitions is foundational for reliable software delivery.
The Build Phase: Activities and Artifacts
The build phase concentrates on producing reliable, reproducible artifacts from the current codebase. Typical activities include dependency resolution, compilation or packaging, and the creation of a versioned artifact set (for example, a binary, a container image, or a library bundle). Build scripts should be deterministic, meaning a given source state yields the same artifact every time. Automated checks—like unit tests, linting, and security scans—are commonly integrated into the build pipeline to catch defects early. Artifacts generated during the build are stamped with version information and metadata so that downstream teams can trace them back to specific source commits. The build not only creates artifacts but also establishes the baseline for what will be released later, ensuring consistency across environments.
The Release Phase: Activities and Artifacts
Release activities focus on getting artifacts from the build stage into one or more target environments while ensuring safety, compliance, and traceability. Key steps include environment configuration, deployment orchestration, release approvals, feature toggles, and rollback planning. Release notes and user-facing documentation are often prepared to accompany the deployment. Emphasis on monitoring, observability, and post-release validation helps teams detect issues quickly and roll back if needed. A mature release process aligns stakeholders, defines gate criteria (such as passing all tests or meeting performance benchmarks), and maintains auditable records of changes, approvals, and environment states. The Disasembl team notes that a well-governed release reduces risk and improves confidence in production deliveries.
Workflows: Monolithic vs Modular Pipelines
Workflows for build and release can be monolithic, where a single pipeline handles code compilation, artifact creation, and deployment, or modular, with separate pipelines for building, testing, and releasing. Modular pipelines offer greater flexibility: teams can evolve the build process independently from deployment workflows, reuse artifacts across projects, and introduce gating between steps without increasing coupling. Monolithic pipelines can be simpler to manage initially but often become brittle as teams scale. The best practice is to strike a balance: maintain a robust, automated build that produces trustworthy artifacts, and pair it with a release workflow that includes appropriate approvals, environment-specific configurations, and monitoring. This separation–but coordination–is what enables scalable delivery in complex systems.
How CI/CD Supports Build and Release
Continuous integration and continuous delivery (CI/CD) underpin both build and release. CI focuses on frequent integration and validation of code changes, triggering builds and tests upon commits. CD extends this by automatically or semi-automatically progressing artifacts through staging to production, guided by policies and approvals. A well-designed CI/CD stack uses versioned artifacts, reproducible environments, and automated rollback. It should also implement security checks, SBOM generation, and vulnerability scanning as part of the pipeline. In practice, CI/CD creates a fast feedback loop: developers see the results of their changes quickly, while operations gain observability and control over deployments. The result is a smoother flow from code to customer value, with reduced risk and faster delivery.
Roles and Responsibilities Across the Lifecycle
Clear ownership is essential for building a reliable flow from code to customer. Developers own the build: writing code, securing dependencies, and ensuring that changes compile and pass tests. Release engineers or platform teams own the release: configuring environments, coordinating approvals, and ensuring deployments meet governance criteria. Shared responsibilities include test strategy, versioning, and rollbacks. Collaboration is aided by shared dashboards, common artifact repositories, and standardized gating criteria. When teams align on responsibilities and maintain traceability across builds and releases, they reduce the chances of bottlenecks and miscommunication during handoffs. The Disasembl perspective emphasizes documented ownership and automated checks as foundations for predictable delivery.
Versioning, Artifacts, and Environments
Versioning is central to both build and release, but the focus differs. Build versioning ensures artifacts are traceable to source and configuration, while release versioning ties deployments to a specific package of changes and environment state. Managing artifacts involves central repositories (for binaries, containers, and libraries) and strict provenance controls to prevent drift. Environment management requires configurations that separate environment-specific settings from code, using feature flags or externalized configuration files. Good practices include environment parity (keeping staging mirrors production), immutable artifacts, and deterministic builds. By harmonizing versioning and environment handling, teams can diagnose problems quickly and rollback with confidence.
Security, Compliance, and Governance
Security and governance are integral to both phases. Build pipelines should incorporate dependency scanning, static analysis, and SBOM generation to surface known vulnerabilities early. Release processes add governance through approvals, change control, and audit trails to satisfy regulatory requirements and internal policies. Protecting the software supply chain means enforcing access controls, maintaining reproducible builds, and ensuring traceability from the codebase to the production environment. Teams should define clear compliance criteria for each release, automate evidence gathering, and validate that deployed configurations match approved baselines. A structured, auditable approach helps organizations avoid incidents and demonstrate due diligence during inspections.
Quality Assurance: Tests, Validation, and Gatekeepers
Quality assurance must span both build and release. During build, unit tests, static analysis, and dependency checks establish a quality baseline. During release, end-to-end tests, integration tests, performance benchmarks, and security validations confirm the product behaves as expected in target environments. Gatekeepers—people or automated checks—enforce thresholds before promotions to production. In practice, a robust pipeline uses build-time tests to filter issues early and release-time checks to confirm runtime behavior in realistic contexts. The aim is to prevent defective code from reaching customers while maintaining speed and feedback loops. Disasembl recommends aligning test strategy with risk: higher-stakes features warrant broader validation and stronger gating.
Metrics and Observability for Build and Release
To understand how well the build-release cycle works, teams track metrics that reflect both speed and quality. Build metrics include time-to-build, failure rate, and reproducibility. Release metrics focus on deployment frequency, lead time for changes, and change failure rate. Observability across environments enhances resilience, enabling rapid detection of anomalies after deployment. Establishing a dashboard that correlates build health with release outcomes helps teams pinpoint where improvements are needed. Consistent metrics support continuous improvement, enabling leadership to make informed decisions about pipelines, tooling, and staffing. In practice, the right data-driven approach reduces guesswork and accelerates reliable delivery.
Common Pitfalls and Remedies
Many teams run into bottlenecks when build times become long, tests drift out of sync, or releases accumulate unvalidated changes. Common remedies include optimizing build performance (caching dependencies, parallelizing tasks), maintaining a clean test suite with fast feedback loops, and implementing clear gate criteria for promotions. Flaky tests, manual steps, and inconsistent environments undermine confidence in releases. Remedy these by adding deterministic builds, environment-as-code, and automated rollout strategies with canaries or feature toggles. Regularly reviewing pipelines for bottlenecks and aligning on ownership helps prevent drift between build and release. Disasembl notes that continuous refinement of pipelines—guided by data and governance—yields more predictable outcomes.
Real-World Scenarios: When to Separate or Merge
Some teams benefit from tightly coupled, single-pipeline approaches during early-stage products with small teams. Others thrive with explicit separation between build and release in large-scale, regulated environments where governance is paramount. The choice often depends on risk, regulatory requirements, and the desire for rapid feedback versus stability. In regulated domains, separations can enforce auditable change control; in fast-moving domains, integration accelerates learning. The strategic decision should consider team maturity, tooling capabilities, and the demand for traceability. The Disasembl guidance is to define a clear philosophy: separate the phases but unify through automation, versioning, and governance so the handoff is painless and auditable.
Practical Implementation Checklist for Teams
- Define clear ownership for build and release with documented handoffs.
- Establish versioning rules for artifacts and deployment packages.
- Implement deterministic builds and reproducible environments.
- Integrate automated tests at build and release stages.
- Enforce gating criteria for promotions and approvals.
- Ensure artifact repositories are secure and auditable.
- Create rollback plans and monitoring dashboards.
- Continuously refine pipelines based on metrics and incidents.
- Maintain environment parity to minimize drift.
- Document changes and provide release notes for stakeholders.
Strategic Takeaways and Future Considerations
The overarching message is that build and release are two sides of the same coin: one creates value through artifacts, the other delivers value through deployment. A disciplined, automated, and governed approach reduces risk while preserving speed. As teams grow, investing in modular, reusable pipelines and strong governance becomes essential. Keep evolving practices around versioning, environment management, and observability to stay ahead of complexity. The Disasembl perspective emphasizes ongoing improvement, automation, and clear ownership as the pillars of successful delivery.
Comparison
| Feature | Build Process | Release Process |
|---|---|---|
| Definition | Converts code into artifacts (compilation/packaging). | Packs, coordinates deployment, and governs environment-specific changes. |
| Primary Goal | Create repeatable, testable artifacts with versioning. | Deliver and monitor artifacts in target environments with governance. |
| Artifacts | Binaries, containers, libraries produced by the build. | Deployed packages across environments with config state. |
| Triggers | Triggered by code changes, automated tests, and checks. | Triggered by promotions, environment readiness, and approvals. |
| Ownership | Developers and build engineers own artifact creation. | Release engineers or platform teams own deployment and governance. |
| Automation Level | High automation for reproducible builds and quick feedback. | Automation for deployment, monitoring, and rollback with approvals. |
| Risks Addressed | Build-time failures, dependency issues, non-reproducible results. | Deployment failures, configuration drift, post-release incidents. |
| Best For | Teams needing fast feedback on code quality and artifact integrity. | Teams needing controlled, auditable deployments with governance. |
Benefits
- Improved clarity of ownership and responsibilities
- Better ability to automate testing and validation
- Enhanced traceability from code to customer value
- Stronger governance and compliance posture
- Faster, safer deployments through repeatable processes
Drawbacks
- Requires extra tooling and maintenance overhead
- Can introduce coordination complexity and bottlenecks
- Potential delays if gate criteria are too strict
- Requires cultural alignment across teams
Coordinate build and release as distinct but tightly integrated workflows
Treat builds as artifact factories and releases as deployment engines. Separate ownership but unify through automation, versioning, and governance to reduce risk and accelerate delivery.
Got Questions?
What is the core difference between a build and a release in software delivery?
A build converts code into artifacts (binaries or containers) ready for deployment, while a release moves those artifacts into production or staging environments with governance, configuration, and monitoring. The two are complementary, not interchangeable, and work best when automated and tightly coordinated.
A build turns code into artifacts; a release deploys those artifacts with governance and monitoring.
Why do teams often separate build and release workflows?
Separating build and release clarifies ownership, allows specialized tooling, and enables risk management through gating and approvals. It also improves traceability from code to customer value and reduces the blast radius of failures by isolating deployment risks from artifact creation.
Separation clarifies ownership and improves risk management and traceability.
What is the role of CI/CD in the build-release lifecycle?
CI accelerates feedback on code changes by automatically building and testing, while CD extends automation to delivery and deployment. Together, they sustain a fast, reliable flow from commit to customer-visible value, with automated checks and governance along the way.
CI builds and tests changes; CD delivers them safely to environments.
How do versioning and artifacts relate to build and release?
Artifacts are versioned during the build to ensure traceability to source and configuration. Release processes tag and deploy specific artifact versions into environments, maintaining a clear history of what was deployed and where.
Artifacts are versioned in build; releases deploy those versions with traceability.
What common pitfalls should teams avoid when coordinating build and release?
Avoid flaky tests, environment drift, and manual gating. Ensure consistent artifacts, deterministic builds, and automated deployments with rollback plans. Regular reviews of pipelines help prevent stale configurations and misaligned ownership.
Watch for flaky tests, drift, and manual steps; automate and back up.
Which tooling supports both build and release workflows?
Many modern toolchains support both build and release, using integrated CI/CD platforms, artifact repositories, and deployment automation. Look for solutions that provide versioned artifacts, environment management, and governance capabilities in a single ecosystem.
Modern CI/CD platforms support both build and release with governance features.
What to Remember
- Define clear ownership for build and release
- Use versioned, reproducible artifacts
- Automate validation at build and release stages
- Guard deployments with gates and approvals
- Monitor outcomes and iterate on pipelines