How to Check Assembly Code for Marvel Rivals: A Practical Disassembly Guide
Learn practical steps, tools, and best practices to check assembly code for Marvel rivals with confidence. This Disasembl guide covers disassembly workflows, pattern checks, and documentation for reproducible results.

By the end of this guide you will know how to check assembly code for Marvel rivals: locate the binary sections, load the executable in a disassembler, verify instruction flows, and compare against known patterns. You’ll use safe lab practices, select the right tools, and document results for reproducibility. This approach emphasizes legality and ethics, reproducibility, and clear labeling so teammates can follow the steps.
Why checking assembly code matters in a disassembly context
According to Disasembl, thorough examination of assembly code helps you understand how software behaves at the lowest level, uncover potential vulnerabilities, and verify that compiled behavior matches documented expectations. In contexts like competitive analysis or educational demonstrations, disassembly provides a verifiable trail from binary to behavior. The goal is not to expose sensitive details, but to learn how instruction sequences translate into control flow, data manipulation, and interaction with the operating system. By focusing on observable, reproducible patterns rather than guesswork, you minimize misinterpretation and mislabeling. This section lays the groundwork for a structured, responsible approach to assembling and checking low-level code.
Core concepts you need before you start
Before you touch any binary, you should be comfortable with a few core ideas. Assembly language is a human-readable layer over machine code; it maps mnemonics to processor instructions. Disassembly is the process of translating binary bytes back into assembly language, which may require handling- endianess, addressing modes, and instruction prefixes. Functional boundaries are not always obvious in optimized code, so pay attention to prologues, epilogues, and cross-references. Pattern recognition matters: common library calls, known compiler quirks, and linker-generated jump tables can reveal structure that isn’t obvious from raw bytes alone. Finally, maintain a consistent naming convention for functions, blocks, and data to support future reviews.
Legal and ethical considerations when analyzing code
Ethical analysis means respecting licenses, terms of service, and applicable laws. Do not analyze proprietary software without explicit permission. When conducting educational or internal research, document the scope, restrict distribution of sensitive material, and avoid sharing exploit details that could enable harm. The Disasembl team emphasizes responsible disclosure and risk awareness, especially when the work touches security-relevant features or competitor products. Always record your sources, maintain version-controlled notes, and seek guidance from a supervisor or legal advisor if you’re unsure about permissible boundaries.
Setting up your toolbox: software, hardware, and references
A solid toolkit reduces friction and increases accuracy. Start with a robust disassembler such as Ghidra, Radare2, or the free IDA options to translate binaries into readable assembly views. Pair this with a hex editor for low-level byte inspection and a notebook or digital document to capture observations. Consider an emulation or sandbox environment if you plan to explore dynamic behavior safely. Keep reference materials handy: opcode maps, calling convention guides, and library function signatures can speed interpretation. Finally, create a reproducible environment checklist so teammates can reconstruct analyses later.
Reading assembly basics and identifying patterns
With the basics in hand, focus on reading assembly in the context of a larger program. Look for function boundaries using prologues and epilogues, identify conditional branches, and map calls to known libraries or OS interfaces. Pattern matching helps: standardized compiler-generated sequences, common optimization tricks, and data-flow patterns (loads, stores, and moves) reveal intent. When you encounter obfuscated or packed code, look for decryption stubs or unpacking loops as potential indicators of hidden logic. Keep a running map of addresses, symbols, and references to support verification.
Validation and documentation practices
Validation means cross-checking observations against multiple perspectives: static view, cross-references, and any available source code or documentation. Document how you identified a function, the reasoning for its boundaries, and the exact instruction sequences that led to conclusions. Use labeled comments in your disassembly, capture screenshots or snippets, and export a minimal, reproducible test case when possible. A well-maintained report includes a call graph, a data-flow diagram, and a checklist showing what was confirmed or refuted. This transparency makes it easier for teammates to reproduce results and spot potential errors.
Case study: example analysis workflow
Imagine analyzing a small routine believed to implement a feature in a rival product. Start by locating the main entry point and listing nearby functions. Step through a few branches to trace what data moves through registers, noting any use of stack frames or local variables. Compare the observed sequence with known compiler patterns and documented libraries, annotating any discrepancies. If you find an obfuscated block, isolate it and test with controlled inputs to observe behavior. Conclude with a concise summary of what the routine does and how it integrates with surrounding code.
Common pitfalls and how to avoid them
A frequent error is over-interpreting isolated instructions without context. Always re-check with a broader code region to confirm intent. Another pitfall is assuming optimizations imply malicious intent; many optimizations are benign and compiler-driven. Failing to document steps leads to miscommunication; maintain a traceable trail of observations and decisions. Finally, analyzing a binary without a safe environment can risk system integrity; use an isolated environment or sandbox whenever possible.
Tools & Materials
- Disassembler software (Ghidra, Radare2, or IDA Free)(Cross-platform options recommended; ensure you can view control flow graphs and function boundaries.)
- Hex editor (HxD, 010 Editor, or similar)(Use for byte-level inspection and patching if needed (non-destructive edits preferred).)
- Sample binary or firmware image(Use legally obtained or your own binaries; avoid proprietary content without permission.)
- Documentation notebook or digital notes(Record reasoning, addresses, and references for reproducibility.)
- Emulation/sandbox environment(Helpful for dynamic analysis without risking your system.)
- Pattern reference sheet(Optional cheat sheet for common compiler or library patterns.)
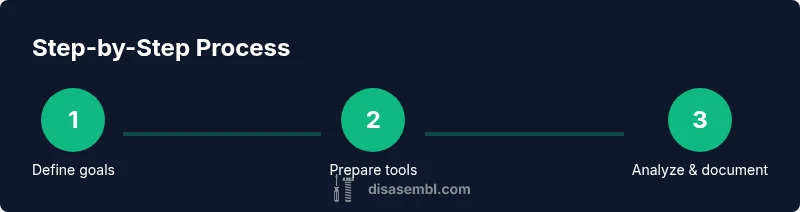
Steps
Estimated time: 60-120 minutes
- 1
Define your analysis goals
Clarify what you want to verify (e.g., function boundaries, control flow, or data handling) and set success criteria. This keeps the analysis focused and reduces scope creep.
Tip: Write a one-sentence goal and return to it if you encounter scope drift. - 2
Collect and prepare a binary sample
Obtain a clean, reversible sample suitable for analysis, ensuring you have permission where required. Create a backup copy before any exploration.
Tip: Verify the integrity of the sample with a hash check and document the source. - 3
Choose your primary disassembler and configure views
Select one tool and set up a consistent workspace: function view, call graph, and data references. Enable annotations and comments to track discoveries.
Tip: Configure color-coding for functions, data references, and jump tables to aid rapid scanning. - 4
Load the binary and locate code sections
Import the binary, identify executable sections, and mark entry points. Note any sections labeled as code vs. data to avoid misinterpretation.
Tip: If sections are poorly labeled, cross-check with headers or a reference map. - 5
Trace initial control flow and map functions
Follow a few call sequences to establish a provisional function map. Record prologues, epilogues, and return patterns for later validation.
Tip: Keep a running diagram of calls and returns to prevent losing track of flow. - 6
Annotate and cross-check with known patterns
Compare observed sequences to common compiler patterns and library calls. Annotate any deviations with hypotheses and supporting evidence.
Tip: Use multiple references to confirm library or API usage before concluding intent. - 7
Validate results with a second perspective
If possible, verify static findings with a dynamic analysis or an alternate disassembler view to confirm conclusions.
Tip: A second tool or view often resolves ambiguous cases. - 8
Document findings into a reproducible report
Create a concise report including goals, methods, evidence (snippets, addresses), and final conclusions. Include steps to reproduce the analysis.
Tip: Version-control the report and export key evidence for team review.
Got Questions?
What is assembly code and why should I check it?
Assembly code is a low-level representation of machine instructions that a processor executes. Checking it helps verify program behavior, security implications, and compliance with expected functionality.
Assembly code is a low-level representation of machine instructions. Checking it helps confirm how software behaves at the processor level and supports safe, informed analysis.
Do I need access to Marvel Rivals’ source to analyze its code?
No. You can analyze compiled binaries through disassembly, but you must respect legal permissions and avoid distributing sensitive content.
You don’t need source access, but you must respect licenses and permissions when analyzing binaries.
What tools are best for disassembly?
Recommended tools include Ghidra, Radare2, and free IDA variants. They provide disassembly, graph views, and scripting support to speed analysis.
Popular free tools like Ghidra and Radare2 offer strong disassembly capabilities and good documentation.
Is it legal to analyze competitor software?
Legality depends on jurisdiction and the software’s licensing. Seek explicit permission when required and avoid distributing proprietary content.
Legality varies by location and license; obtain permission when needed and avoid sharing sensitive material.
How long does a typical assembly analysis take?
Time varies with binary size and complexity. A focused analysis of a small routine can take 30–90 minutes; larger projects require longer sessions with careful documentation.
It varies, but small routines often take under an hour; bigger analyses can take several hours with thorough notes.
How should I document my findings?
Create a reproducible report with goals, steps, evidence (snippets and addresses), and conclusions. Share the document with teammates for review.
Document the goals, methods, and evidence clearly so others can reproduce your results.
Watch Video
What to Remember
- Define clear goals before starting analysis
- Use multiple tools to validate observations
- Document every step for reproducibility
- Be cautious with obfuscated or packed code
- Adhere to legal and ethical guidelines